Security Practices
Copyleaks prides itself on taking data security and privacy very seriously. We make it our top priority to protect our clients, our system, and our infrastructure, using the highest security levels.
Data safety anxiety is common in today’s digital age of massive data collection and minimal data security. Preventing unauthorized access to personal information is an essential issue throughout the world. Despite following cybersecurity best practices, the chances of a data breach are not impossible. To alleviate our users’ fear regarding data security, Copyleaks provides military-grade 256-bit encryption with an SSL connection, ensuring your document content and account are always safe and secure.
It is not uncommon for hackers and unauthorized third parties to try stealing users’ sensitive information online. That’s why we’ve increased security and data protection measures to ensure our users’ safety, as outlined in our law-abiding legal statement that states the terms and conditions of our website’s services. This document provides a detailed list of the types of personal information stored on our website. Although we have cookies, these cannot perform any action on your mobile device or desktop. The cookies are kept only for improving your experience.
Our website’s cookies do not transfer personal information from your device to any other system unless another system utilizes the cookies served by Copyleaks. Such third-party cookies are beyond the Copyleaks’ control, and it depends upon the settings chosen by the user. You have the option to adjust the security settings of your computer/system and restrict the usage of such cookies by accessing your account on our site and modifying settings in your browser.
At Copyleaks, we work tirelessly to find and fix all security bugs to ensure the safety of your personal information. Our professional research and development team routinely scans our system for security issues. In addition, Copyleaks works closely with external security teams to execute Penetration Testing on our systems. We work round-the-clock to optimize our system, improve users’ experience, and eliminate security concerns.
It is common to encounter concerns when signing up for online services, particularly those that fail to outline security policies. However, at Copyleaks, we prioritize our customers’ data safety over anything else. Our Cloud-based software offers a unique feature rooted in security, allowing users to sign in from any device or web browser through a robust authentication process. To increase security practices on the users’ end, we recommend our users use strong passwords combined with multi-factor authentication.
We do not allow users to sign in from devices ruled as suspicious. In addition, we alert users regarding unauthorized sign-ins and seek confirmation from the user about their authenticity. These are only some of the practices we follow at Copyleaks to enhance our services and maintain watertight security for all our customers.
This guide includes the main security overview of how Copyleaks is keeping data safe and secure.
System Architecture
Copyleaks’ architecture is built for Cloud hosting. All of our product components are stored in the Cloud, maximizing data safety. Using the Cloud, Copyleaks can maintain flexibility in terms of load through our built-in security mechanism designed by Google Cloud top engineers.
Copyleaks’ system was designed and built using Microservices architecture. Through this design, our service is continuously updated and optimized for our users. These updates include new features, security fixes, and bug fixes. Furthermore, all these infrastructure updates are completed with zero downtime. So, for all Copyleaks customers, this process is seamless and without any service disruptions.
Data Centers
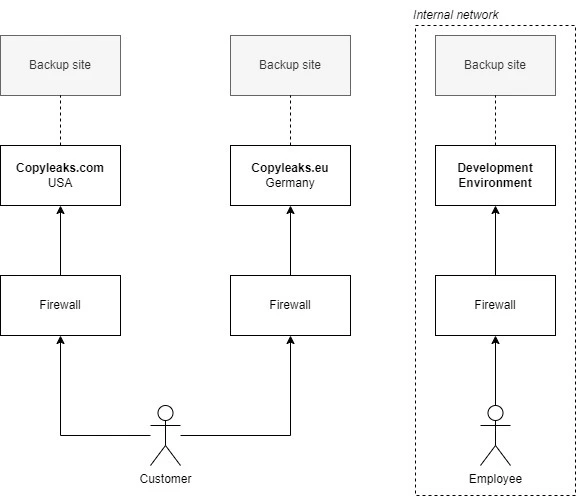
Copyleaks data centers:
- Copyleaks.com – located in the USA.
- Copyleaks.eu – located in Germany.
Copyleaks infrastructure is hosted on Google Cloud and highly secure with physical protection 24/7/365. Read more about the Google Cloud Physical Protection Policy.
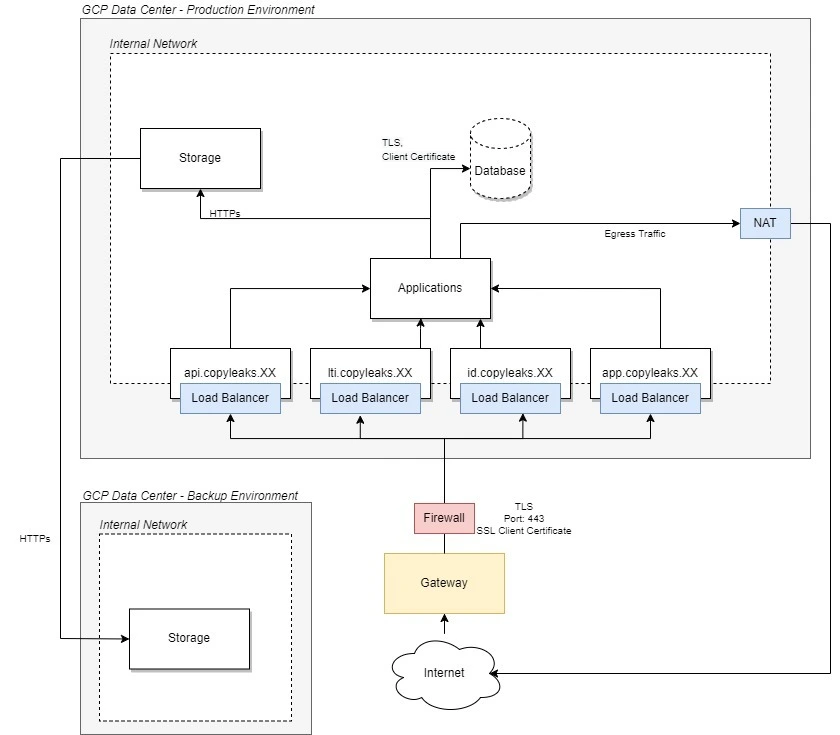
Data Center Architecture
Product Security
The security measures of Copyleaks are aimed at checking systemic vulnerabilities and finding immediate and long-term solutions. Our professional team routinely scans and reviews access points to ensure data privacy at all levels. All our products are designed to enhance our users’ experience while maximizing and preventing information loss. Being a cloud-based software application, Copyleaks helps you keep information safe in the Cloud backup zone. We ensure that your information is not used by any other systems/applications while using our platform until you have given explicit third-party permissions or enabled pop-ups from those sites separately.
Network Security
Copyleaks software/platform communicates through an internal company network. All of our components use this network. Copyleaks employees do not have access to this resource unless it is specifically needed to operate the system. Further, Copyleaks employees use an independent network structure, which connects the Employee and Internal networks through a secure VPN. Internal firewalls monitor employees’ access and limit access as needed. All incidents reported are sent immediately to the data prevention/security team. All of the incoming connections to the internal network are secured. To get permission to access the internal network system, the requestor must prove his/her identity using an SSL client certificate. After proving the requestor’s identity, the system enforces limitations on who can access each component. Unfamiliar connections from untrusted sources will be blocked and immediately reported for further investigation. The communication inside the internal network is secured using TLS v1.2 or newer. The security team continually updates and enhances these security protocols.
Data Security
Data safety is an integral part of Copyleaks security mechanisms. Data is encrypted both in transit and in rest. In rest, all of the saved data is encrypted. We use AES-256bits encryption to encrypt data. The key is managed by Google Cloud and is rotated automatically as needed. In transit, all of the data is transferred using only secure channels (HTTPs). The data backup procedure takes place daily. We store backed up data in our secure US-based data centers for at least four months, giving you peace of mind.
Data Collection Policy
We keep two copies of the customer’s data. Each of our data centers are being backed up on a daily basis. The backup is being stored on a different Google Cloud datacenter, to ensure data safety in case of catastrophe.
Our data backup was designed to solve problems caused by the infrastructure (e.g. earthquake) and problems caused by mistakes of Copyleaks employees. In contrast, problems caused by users, e.g. user accidentally removing a file, is not part of this policy scope.
Applications Security
We make security our highest priority when writing our applications. To achieve a high-security level, we:
- Routinely run vulnerability scans of our system components.
- Update the security of our products regularly.
- Use static code analyzers to detect problematic codes.
- Anonymize any individual data while analyzing and ultimately improving our security standards.
Our applications are typically updated for any security threats every few days and at a very high rate. This high rate and frequency allow us to react fast to any change needed within our infrastructure. All this with zero downtime–which provides a seamless and uninterrupted service to the end-user.
Monitoring
Our system is continuously monitored round the clock, 24/7. This allows us to respond instantly as soon as we detect any downtime incident. We monitor our system every 5 minutes from 5 different regions around the world: Europe (Belgium), Asia Pacific (Singapore), South America (São Paulo), and the United States (Iowa, Oregon, Virginia). Global monitoring checks ensure optimized services to our customers around the world. This multi-location downtime reporting approach allows us to identify quickly if a specific geographic region has network problems. Like any other software system, system incidents may occur from time to time. To keep the Copyleaks user community informed of such occurrences, we maintain a separate website. Copyleaks users can stay up to date with the system downtimes, if any, on status.copyleaks.com. During our onboarding, we highly recommend our users to subscribe to live status updates on this website. As a matter of record, Copyleaks services run at an all-time average of 99.95% uptime, which is an impressive industry record.
Employee Practices
By default, Copyleaks agents do not have access to customers’ submitted files. If the customer wants to allow Copyleaks agents to get access to his, he needs to explicitly allow this and limit the access by a time period. After granting access, some Copyleaks agents will have access to customers’ scans.
We have an experienced team for handling user accounts. We do not take employee security lightly. Our professional experts work tirelessly to ensure Copyleaks’ services run smoothly and are only allowed access to information pertaining to their responsibilities. Copyleaks primarily access users’ data to improve their service and address any concerns. We ensure that all employees validate their identity through a strict security process before they gain access to our system. Employees have to mandatorily follow a 2-factor authentication process to eliminate wrongful access risks. Copyleaks also enforces a complex password policy, ensuring that passwords being used are made up of randomized characters, alphabets, and other elements. There are further checks, balances, and randomized audits made on company employees to eliminate data breach possibilities.
All employees do not have access to all the user data, and this has been done on purpose so that no user data can be readily made available to any employee. Employees are also required to sign into their web browsers using company emails, allowing the Copyleaks security team to monitor the employees’ activities as per set protocols.
Compliance
- The Copyleaks data centers collect and process the information that you submit while creating your account as per the Israeli Privacy Protection Law, 5741-1981. We comply with this protection of privacy law to safeguard the data of our users.
- The EU data center (copyleaks.eu) is GDPR compliant.
- PCI DSS – We do not store, process, and\or transmit cardholder data. Copyleaks use Stripe Inc to execute payment transactions.
Third-Party Vendors
Our services provide opportunities to connect with external services platforms. These third-party links do not fall under the ambit of the Copyleaks data security system. To protect your data, read the statement of the third-party sites before providing any personal information.
More Information on Copyleaks Data Security
We are looking to enhance information security for our users. If you have any security concerns regarding your data, you can report it to our team. As a registered user, you can send a screenshot of your security incident from your registered email ID to [email protected] You can also add any other relevant information related to the security breach in the email.
If you have any questions regarding our security measures, you can send your query to [email protected]. If you have any queries on our Privacy Policy or Terms and Conditions, you can reach out to our support team using your Copyleaks email ID, and we will address your concerns as soon as possible.
As always, we are doing our best to eliminate cybercriminals’ risk and keep your sensitive information protected at all costs. If you ever feel as though your account has been compromised, please contact us immediately through email. You can also delete your information while disabling your account by visiting https://id.copyleaks.com/security/delete-internal-data.
Vulnerability Report
We perform both vulnerability scans and penetration scans on a regular basis through Google Cloud. We always welcome and encourage comments from our users if they have identified a vulnerability of any kind. You can submit a report to Copyleaks with the following details:
- If you are a registered Copyleaks user and the email address associated with your account.
- Screenshot of issue.
- Any other information you want to share.
- Read more here.